Safetica NXT, next-gen SaaS DLP, helps you keep your sensitive data out of the wrong hands by detecting security risks and preventing incidents, from day one. Let's take a look at several universally applicable best practice settings that can significantly improve your Safetica NXT experience.
We have designed Safetica NXT that it provides the highest level of data protection while minimizing the load on users. Try these five steps to learn, how to ensure the maximum data security with the minimal burden on the IT department by slashing the number of false positive alerts.
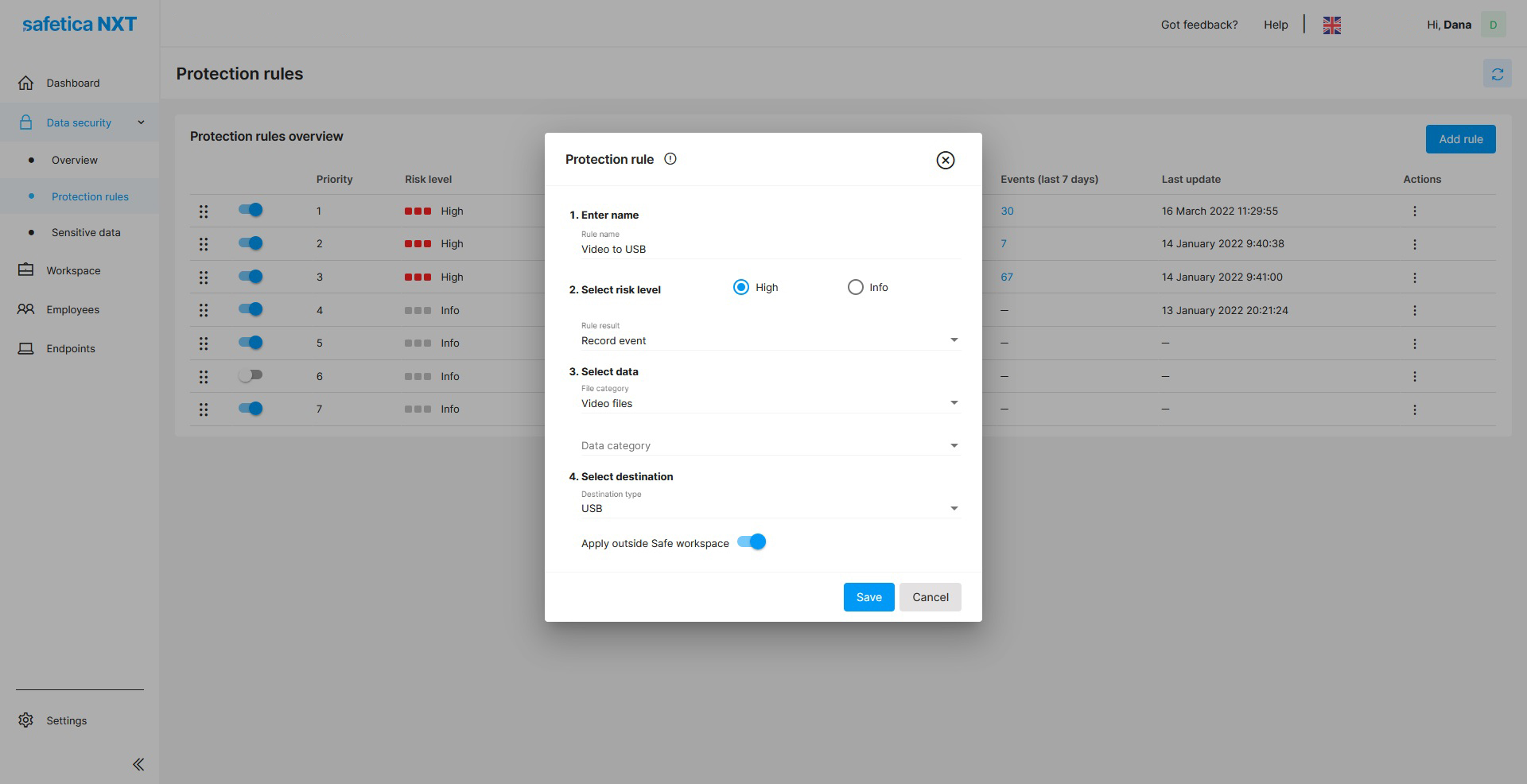
1. Set up your Protection rules
Safetica NXT allows you to detect and block security incidents in outgoing data flow to prevent the loss or misuse of your data.
Automated smart scanning offers the first level of protection. Furthermore, you can create your own protection rules to explicitly decide what action to take on an endpoint when an incident occurs. This incident may be uploading a document to public file-share services or sending an email with an attachment containing a file with account numbers.
Three Protection rule options:
- silently record the action,
- notify the user about it and let them decide whether to finish the action or not,
- completely block the incident.
2. Maintain your environment
Your perimeter is only as secure as its endpoints – i. e., your users' devices. Maintain your environment by enrolling new endpoints in Safetica and troubleshooting the ones with issues. It is also important to keep all endpoints up-to-date with the newest version of Safetica Client.
3. Detect risky events
Detect risky events using on our automated smart scanning and your custom Protection rules. Safetica NXT assigns a risk level to individual events based either on predefined Protection rules or your own custom rules that address the specifics of your environment.
To further increase risk level accuracy, you can create a data category that will automatically search for selected sensitive data in outgoing files (predefined algorithms, regular expressions, or keywords).
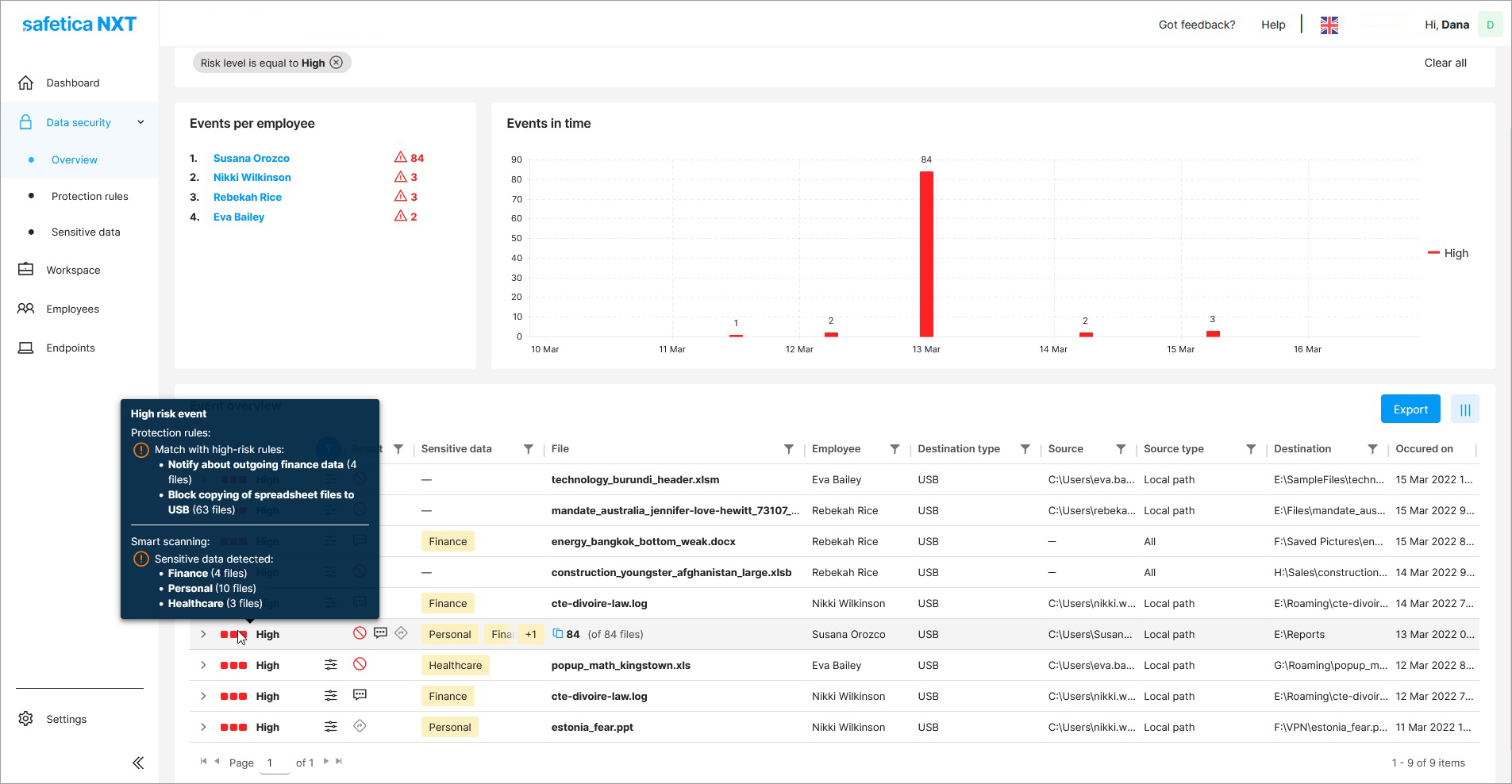
4. Analyze discovered risky events
Analyze and investigate discovered risky events in minute detail. To keep assigned risk levels precise and reliable, it is important to review the discovered events and reclassify them if necessary.
To avoid classifying data transfers performed within the company environment as high-risk events, we recommend that you define safe email domains, external devices, and websites. You can do so in the Workspace section.
5. Act fast and prevent data loss
Prevent data loss with a fast response. Get notified about risky events immediately.
If you follow these steps in your setup, your environment will be correctly configured and you can effectively use real-time notifications. Use Protection rules to notify or restrict users from leaking sensitive data from your safe company environment.
Are you interested in Safetica NXT features and improvements? Take a look at this changelog or the Safetica NXT blog page.
Next articles

Safetica NXT – SaaS DLP introduction
Safetica NXT is a cloud-native DLP solution with super-easy management and a flexible subscription. Its risk-driven incident detection is powered by data analytics.

