The year 2017 has seen countless attacks on sensitive data, a huge buzz around GDPR, as well as new threats. Let’s look back at what the year brought us in security and get a glimpse at what 2018 has in store for us.
2017: Serious data leaks, GDPR and new threats
We’ve witnessed several high-profile ransomware attacks where companies like Yahoo, Equifax or Uber lost their sensitive data. And even though these are all large household names, almost half of all data breaches happened to smaller companies. It’s becoming increasingly important to protect data even in your company has single or double-digit employee count. Cyber attacks can actually cause more damage to you than to the largest firms. A security issue or loss of reputation is simply more difficult to handle in a small company and it’s hard to rebound from that.
GDPR? Companies have neglected preparations
GDPR as the strictest data protection regulation ever resonates mainly in the European Union. However, companies seem to underestimate the preparations. Our November poll among 80 Czech companies has shown that 79% of them are still not prepared for GDPR. The thing is, unless the companies have started with the preparations several months ago, they’re very unlikely to make it without skilled consultants. The regulation comes into action on May 25, 2018. The requirements are strict and the fines for non-compliance are high.
Number of attacks, damages and expenses in data protection are rising
According to a study conducted in 2017 by Ponemon Institute LLC and Accenture, the average annual expenses in data security are 11.7 million USD. Cyber security expenses have increased by 22.7%, while the average number of data leaks is growing by approx. 27% every year. In the United States alone, there were 1579 reported data leaks. The real number is probably much higher.
Overall damages caused by cyber attacks per country in 2016 and 2017. Source: Ponemon Institute LLC and Accenture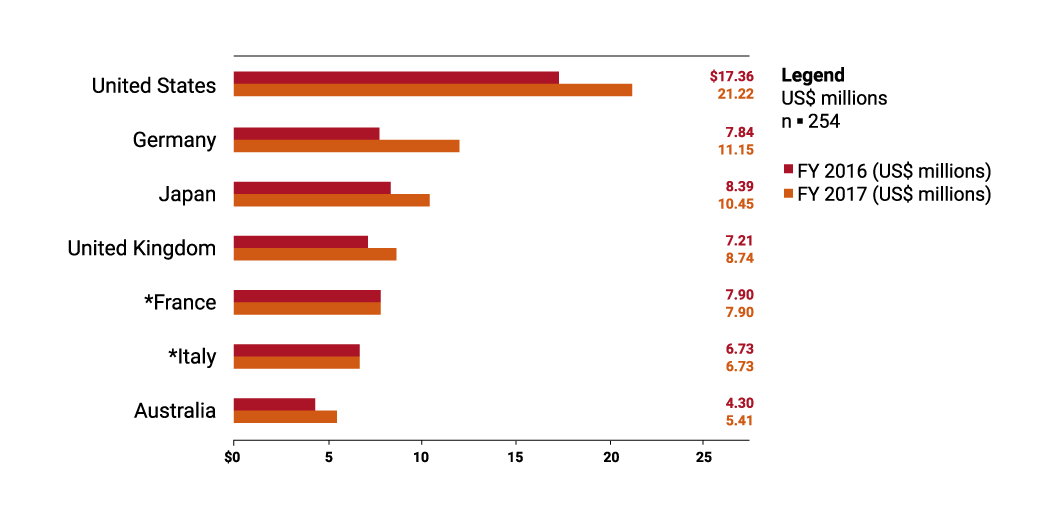
The numbers are grim, but cyber security companies are quick to fight back. The products are getting better to resist increasingly complex attacks.
New threats
Cyber attackers have started targeting mobile devices instead of computers and laptops. They target employees‘ unawareness as a vector of attack bypassing even the most complex security software. New attacks target completely unprepared IoT (Internet of Things) devices such as smart appliances, smart homes, etc. It’s positive that even small companies have started to realize the threat to their data and their company itself, if the data got in the hands of their competitors. This is demonstrated by increasing amounts the firms are willing to spend on cyber security. They are starting to prefer preventing fires to putting them out, and this is great.
2018: Growing expenses, more serious attacks and employee crisis

Number of cyber attacks grows with every year, whether it is data leaks, ransomware attacks, migration of desktop malware to mobile devices, or IoT attacks. This forces companies to invest more into data protection. They realize that vast majority of their data and documents are stored only in digital form. This further increases the impact of cyber attacks on the lives of people and companies who’s information can be stolen and misused.
New legislation shapes the market with data protection products
The need to protect from cyber attacks is doubtlessly driven also by the attention this topic gets by legislators. Whether it’s the new Amendment Privacy Act in Australia, GDPR, or The Network Information Security Directive. Osterman Research says that companies will invest the most in DLP software in preparations for the GDPR which is coming into effect on May 25, 2018.
Data Protection Technologies That Organizations Will Spend More On During the Next 12-18 Months to Specifically address the GDPR. Source: Osterman Research, Inc.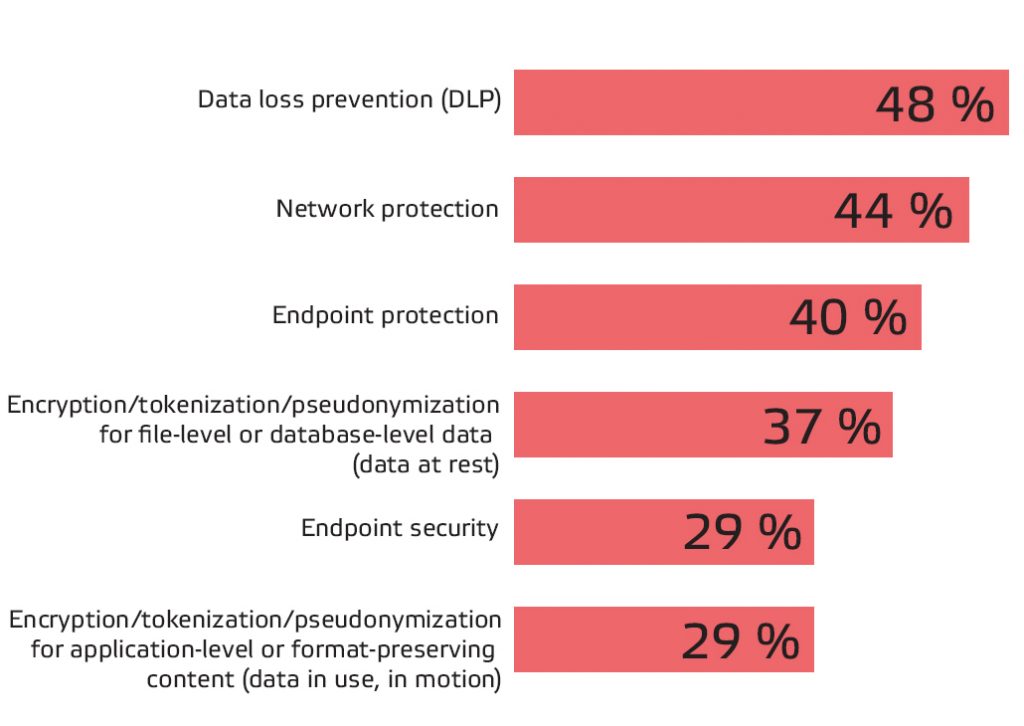
Protection against attacks has to be automatic
The increasing number of attacks makes it clear that any security measure has to be fulfilled automatically, and that data has to be automatically protected. This principle is obeyed also by Safetica DLP, which initially monitors internal company processes, and then enforces security policies that not only stop data leaks, but more importantly prevent them.
The weakest link in cyber security is always the human
Kevin Mitnick, the world-renown hacker and a cyber security expert in KnowBe4 has said: “You could spend a fortune purchasing technology and services, and your network infrastructure could still remain vulnerable to old-fashioned manipulation.” This is why we at Safetica always look at how employees work with important data and thus help them to be safer.
The biggest topic in 2018 will be employee education to teach them to be safe when working with any type of sensitive data. That’s why we will continue with employee trainings for our customers, and not only them.
Manufacturing firms will get on cyber criminals watch lists
While cyber attacks of 2017 were aimed primarily at healthcare, Cybersecurity Ventures predict that the focus will move to manufacturing firms. And not just the large ones, but those smaller ones who typically don’t spend enough time and money on cyber security. Despite this, Cybersecurity Ventures forecasts that small companies will look at ways to prevent the attacks with preventative measures, including DLP software.
We don’t doubt that a hard but successful year is ahead of us. Be there with us! Follow us on Facebook or LinkedIn, and follow this blog.
Sources:
Cost of Cyber Crime Study 2017, Ponemon Institute LLC, Accenture
Cybersecurity Market Report 2017, Cybersecurity Ventures
Cybercrime Report 2017, Cybersecurity Ventures
GDPR Compliance and Its Impact on Security and Data Protection Programs by the Osterman Research Center
Equifax data breach
Yahoo data breach
Uber data breach
Do you want to read more?
https://www.safetica.com/blog/our-successes-in-2017-and-our-plans-for-2018/?utm_source=blog&utm_medium=blog&utm_campaign=january_newsletter&utm_content=safetica_success
https://www.safetica.com/blog/7-reasons-to-enjoy-safetica-7-8/
https://www.safetica.com/blog/ransomware-spreads-across-europe-you-never-know-when-it-can-attack-how-to-defend/
Next articles

Securing Slack: The Power of Data Loss Prevention
Slack has become the go-to cloud-based collaboration tool for companies of all sizes. Read how to secure Slack with Safetica.

