Implementation of complex software (like Data Leak Prevention) usually stands for a challenge, especially for SMB companies without a dedicated IT department. However, rules have changed and deployment with Safetica 7 can be achieved only in 3 steps, even though there is a new component - WebSafetica (try demo here) - which runs on an MS IIS platform.
So what Safetica 7 actually brings to help you?
- Single installation package – installation and configuration of individual components are hidden under the hood, so all there’s left for the administrator to do is to launch the setup package on the server and follow the wizard
- Seamless integration of all components – all components are automatically and securely interconnected and will maintain this connectivity during normal administration tasks, like changing passwords
- We’ll help you with the environment – setting up server-based software is often an art form. We’re ready for many corner cases, take care of the back-up plans for your SQL database, configure the web server for you, and more
- First configuration and deployment – we walk you through the final installation steps and guide you during the deployment of our agent software on your users‘ computers
- Auditing profiles – predefined configuration sets give you a choice of the audit level to match your needs. All there’s left is to sit back and watch the data flow throughout your company
- Recommendations and warnings – in addition to audit data, WebSafetica dashboard gives you recommendations and warnings to help you get the most out of Safetica
For installation and configuration, you can choose to have full control, use your own database and web server and keep tabs on the deployment. Or you can follow the approach taken by one of our SMB customers - using express installation to install Safetica 7 in 3 easy steps.
Let's get practical: Deploying Safetica 7 on 100 PCs and 1 server
Step 1 – Express installation
Start the Safetica installation package on your Windows server and choose the Safetica installation (recommended) option. Decide if you also want to install WebSafetica, which will enable the MS IIS server for you.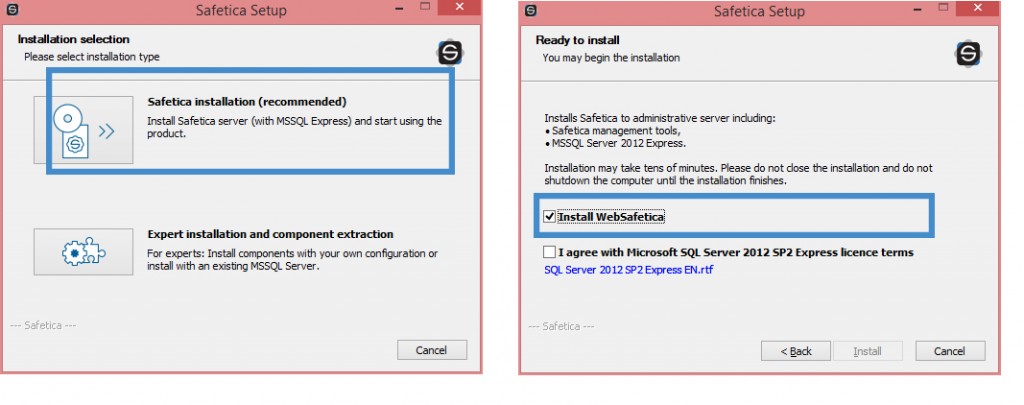
Step 2 – Connecting clients
Safetica Console starts automatically after installation and checks its connectivity to all components and to the outside world (SMTP server, Active Directory, etc.). Next, you’re given a pre-configured client package which needs to be installed on at least one endpoint. As soon as the client connects to the server, you’re done with the setup – you can install any additional clients at your own pace*.
*There are more ways to distribute the additional clients into a large network, e.g. using a GPO policy or any other remote execution tool. This is done only once – any future updates are automatic.
Step 3 – Activating Audit
The final step to a successful audit is entering the license number and choosing the audit level. Check out the image to see what your options are. The results will start coming in now and you can enjoy the new insight you have into your company.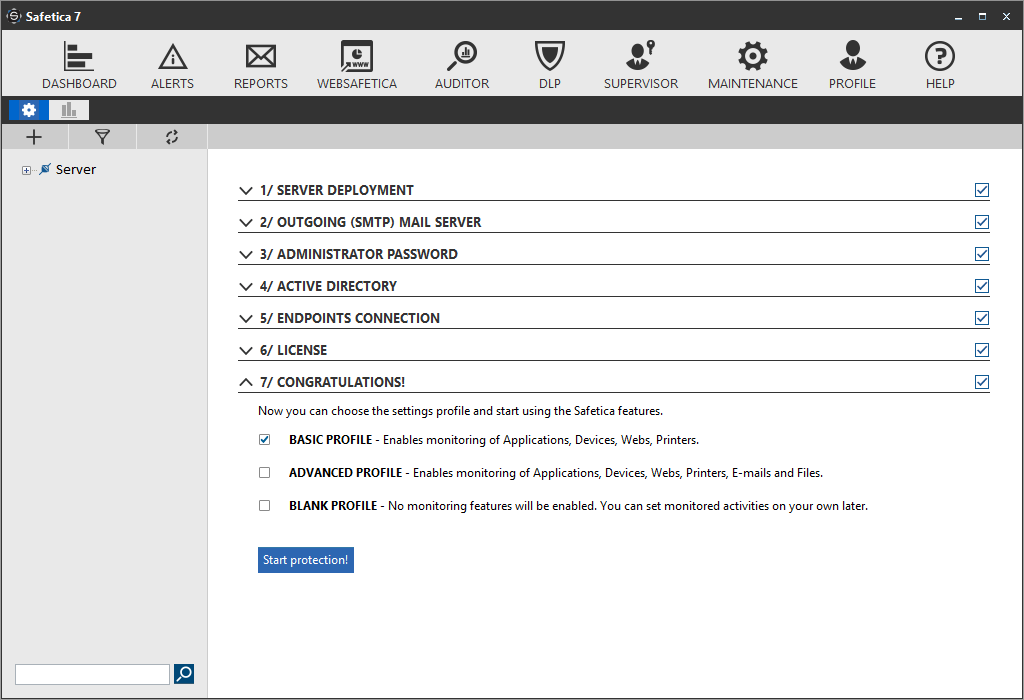
Do you know what’s happening with your data? Now that we’ve released Safetica 7 you can’t blame your lack of insight on lack of time.
For Zbynek software development is a synonym for art. He sees the magic in climbing and is a total ice hockey freak. At work or at play, the challenge is the name of his game.
Next articles
Block and Protect Your Sensitive Data in ChatGPT Using Safetica
To minimize the risks of data loss associated with ChatGPT, Safetica offers an effective solution.

